Lately it seems there has been no shortage of critical vulnerabilities being discovered in commonly used software. In the past couple of weeks alone, Adobe has had to release patched versions of Flash to address a trio of publicized zero day vulnerabilities. While as a host that doesn’t really impact us directly, it should be a top priority for anyone browsing the web. The vast majority of end-user computer infections come from malicious content taking advantage of such vulnerabilities. These can often lead to your login information being compromised which certainly does become an issue for us. As always, please be sure you’re staying up-to-date with these Flash patches as well as those for your operating system, web browser, Java, etc. Continue reading
Category Archives: Security
Behind the Scenes: POODLE SSLv3 & Network Speedtest
As you may have heard, in October a new vulnerability was disclosed in SSL version 3 that was dubbed POODLE (Padding Oracle On Downgraded Legacy Encryption). This allowed an attacker to read SSLv3 encrypted data via a man-in-the-middle attack. It has long been standard to disable SSLv2 and as a result of this new disclosure many providers, including us, have opted to disable SSLv3 as well. Disabling SSLv3 was really long overdue anyways and only used for legacy support of older operating systems that have long reached their end of life, such as initial releases of Windows XP. Any recent OS or software will instead use a version of TLS to connect which is now the only option that our servers permit. Aside from a couple of very minor cipher issues which were quickly remedied, we’ve experienced no problems with the deployment of these changes back in October. Ultimately this is just another small part that shows our ongoing commitment to security here at Dathorn, where keeping your data safe and secure is a priority.
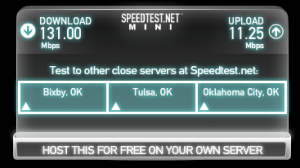 In other unrelated news, we have added network performance testing information to our network page. We frequently receive requests for information on how to test our network connectivity from a client’s location. To help make this process easier we’ve added this information directly to our website and have even setup a speedtest there. The image above shows some sample results from my own cable connection at home. Does anyone with Google fiber want to show off a bit?
In other unrelated news, we have added network performance testing information to our network page. We frequently receive requests for information on how to test our network connectivity from a client’s location. To help make this process easier we’ve added this information directly to our website and have even setup a speedtest there. The image above shows some sample results from my own cable connection at home. Does anyone with Google fiber want to show off a bit?
Drupal SQL Injection Vulnerability – CVE-2014-3704
On October 15th a very serious SQL injection vulnerability was discovered in Drupal that exists in all 7.x versions prior to 7.32. The severity of this vulnerability led to quick exploitation of it within approximately 7 hours of it having been publicized. Fortunately the provided patch to address this issue was quite simple and easy to apply. In fact, the patch only changed one line of code in the includes/database/database.inc file. Because of this we opted to go ahead and pro-actively apply the patch to all installations of Drupal 7.x on our servers. In less than an hour we had protected all of our clients’ Drupal installations from being exploited by this vulnerability. Beyond that it helped to protect our servers from attackers that were exploiting this vulnerability to run other malicious scripts. Affected clients should still upgrade their Drupal to the latest version as soon as possible.
Overall we were very pleased that this was so easily addressed on our end and we will certainly look into options like this going forward as new vulnerabilities in popular scripts are discovered. This incident shows how important it is for you to stay on top of script, plugin, and theme updates. Within a mere 7 hours of publicizing this vulnerability, it was being actively exploited. We highly recommend that you sign up for security related mailing lists for the scripts that you are using if they are available. This will give you the best chance at protecting yourself when (not if) a vulnerability like this comes to light.
Behind the Scenes: Shellshock & PHP 5.4
Here’s another quick update on what’s been going on here behind the scenes at Dathorn. As you may have heard, critical bugs were discovered in the popular Linux shell, bash. This event, dubbed “Shellshock”, started to publicly unfold about two weeks ago.
 The details of these vulnerabilities can be a bit difficult to follow given the number of different patches that were posted. It even required a few quick, consecutive updates from some Linux distributions just to get it right. It seemed like each time a new patch was released someone else was able to poke holes in it, finding new methods to exploit and turning bash into a bit of swiss cheese. Continue reading
The details of these vulnerabilities can be a bit difficult to follow given the number of different patches that were posted. It even required a few quick, consecutive updates from some Linux distributions just to get it right. It seemed like each time a new patch was released someone else was able to poke holes in it, finding new methods to exploit and turning bash into a bit of swiss cheese. Continue reading
Quick Look: WordPress Security Plugins
Securing a WordPress installation is certainly not a new topic. A quick Google search will turn up a large number of guides on how to go about doing this. Many of these have great information already but this task can often seem tedious to those that are inexperienced or don’t have a lot of time to spend on it. Given that WordPress is by far the most popular script that our clients use on our servers, I wanted to quickly highlight a couple of plugins that we find very useful in mitigating various issues that we’ve observed.
Better WP Security
The Better WP Security plugin offers a set of very straight forward steps that you can follow to help secure your WordPress installation as you can see below. Continue reading
Safe Web Browsing Practices
A couple of our recent posts have covered how to keep your login information secure and how to secure your local environment. In the latter we briefly mentioned how important it was to browse the web safely. Malicious content being served from a website is by far one of the biggest and most common threats to the security of your computer. The best advice that I can offer concerning safe web browsing is simple: trust nothing.
It should come as no surprise that browsing unsavory websites, such as those containing adult or pirated content, comes with risks of infecting your computer. Unfortunately this same potential exists with every single website out there. Some might think that since they are visiting a reputable company’s website that it is safe and that is not the case. Back in February NBC’s website was compromised and ended up serving malicious content to users. Just this past August the New York Times’ DNS was hijacked leaving near endless possibilities for attackers to abuse. Again my advice on handling this would be to trust nothing. Continue reading
Securing Your Local Environment
A couple of months ago we briefly covered how to help keep your login information secure. Some of the biggest threats to maintaining secure login information are your own computers and devices (phones, tablets, etc.). It is unfortunately quite common for a computer to be infected and any login information used on it compromised as a result. Here are a few important things to consider which can help to greatly reduce your chances of being infected.
Patch / Update Your Software
This is the golden rule as far as security is concerned and there really is no excuse to not be keeping your software updated. Attackers are quick to target new vulnerabilities so it is very important that all patches be applied in a timely manner. The three main things to keep note of would be:
- Operating System – It doesn’t matter if you use Windows, Linux, or even a Mac. All of them can be vulnerable and need to be kept updated.
- Anti-virus Software & Definitions – Should anything get through, your AV software needs to be current so that it has the best possible chance of preventing an infection.
- Browser Related Software – This would include your web browser of choice along with all plugins. Flash, Java, and Adobe Reader are all commonly targeted by malicious websites. Continue reading
Keeping Your Login Info Secure
Your login information is the key to your hosting account. Much like your car keys, house keys, and ATM pin, you don’t want your login information stolen. We all know that a strong password is a good idea and that we shouldn’t be writing down logins on post-it notes next to our computer. Those topics have been well covered for many years. We’re going to cover a few of the less obvious, although equally important, aspects to keeping your login information secure.
Encryption
Login information should always be submitted over SSL. This is easily confirmed by looking for “https” in your browser’s URL bar. Extended validation SSL certificates, like the one we use for our main website, portal, and billing system, will even show up green in the web browser as seen below.
Being Caged Up Isn’t Always Bad: CageFS
My wife and I are both dog lovers and finally rescued our first dog, a Golden Retriever named Carson, two years ago. Carson was a puppy at the time and we were determined to have a well behaved dog so we began crate training him from day one. As a dog owner, you have to understand that a crate (or cage) isn’t just a means of punishment. It is intended to be a safe place for the dog to escape to while also providing safety to the dog and your belongings while you’re away. As it turns out, Carson loved his crate and would even willingly take a nap in it on occasion.
We could leave the house knowing that Carson was safe and secure in his own environment. If we had not put him in his cage, things would have turned out differently. Continue reading
Malware Scanning of Web Content
Securing an online presence can be one of the most difficult tasks that our clients face. We spend a tremendous amount of time keeping a watchful eye on security advisories, applying patches, etc. just to make sure our servers remain secure. This is often very hard for resellers and web developers alike to keep up with.
For instance, let’s take your average WordPress based website. Not only do you have to make sure the WordPress core stays updated but you also have to do the same for all plugins and themes that are being used. It is very common for a WordPress site to have more than 10 plugins and a handful of themes installed at once. Fortunately, WordPress has a good interface for managing and installing these updates easily. Often times everything can be upgraded in just a few clicks. However, this still requires that someone login to the WordPress admin interface and perform the upgrades. For resellers managing hundreds of sites this can be tedious at best and it is easy for one to get overlooked.



